Security checklist for AI-generated apps: auth, RBAC, payments
AI accelerators are shipping code faster than your review queue. Whether you build with a workflow automation app builder, scaffold UIs via an AI web design tool, or push cloud deployment with Slashdev Cloud, this checklist hardens what the generator creates.
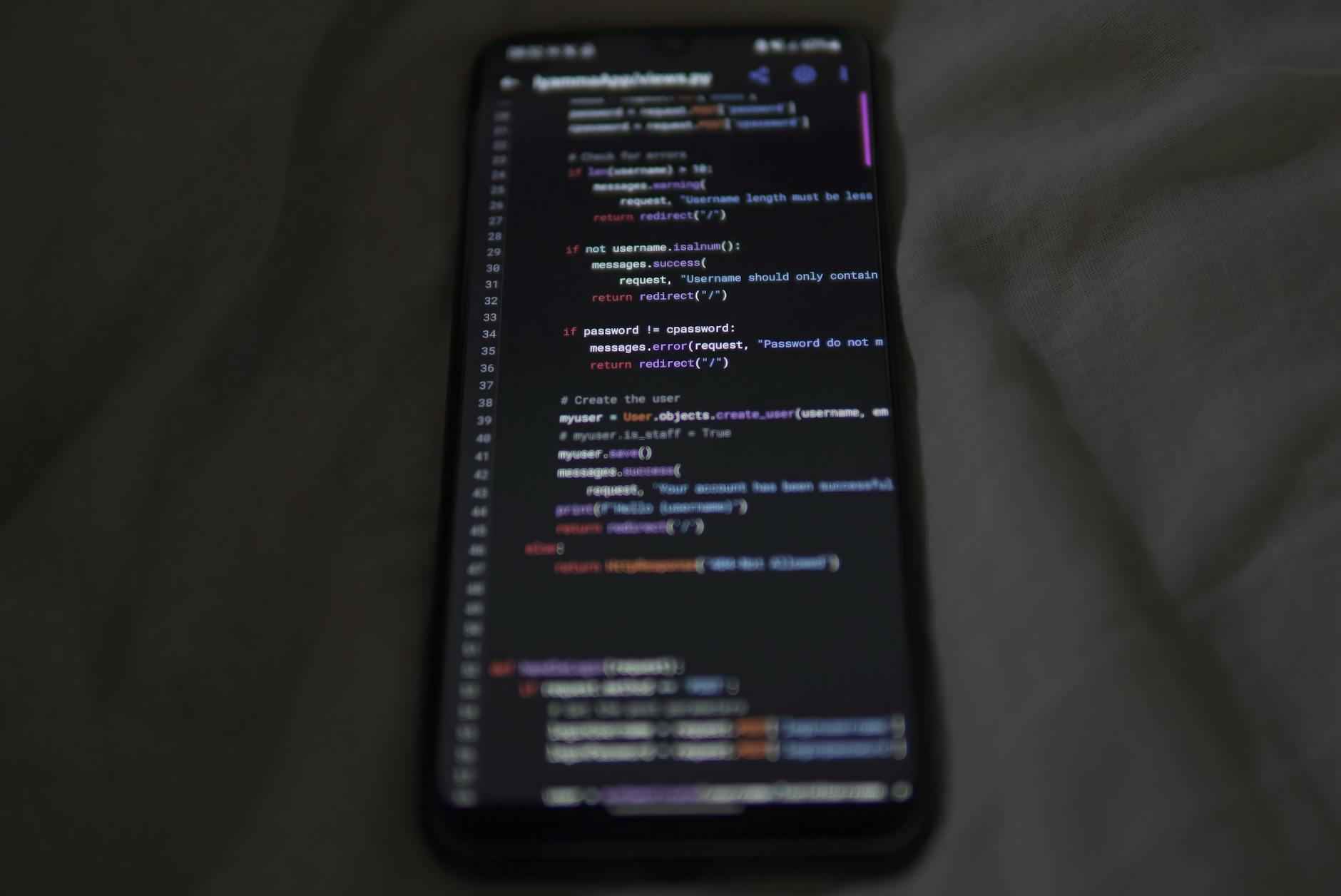
Authentication and session security
- Adopt OIDC/OAuth2 with PKCE; prefer SSO (SAML/OIDC) for enterprise tenants; enable MFA by default and allow FIDO2 passkeys.
- Issue short-lived access tokens (5-15 min), rotate refresh tokens, bind tokens to client and audience, and maintain a revocation list.
- Use HttpOnly, Secure, SameSite=strict cookies; implement CSRF tokens on state-changing requests; validate redirect URIs strictly.
- For service-to-service flows, use mTLS or workload identity; never ship static secrets in code-pull from a managed secrets store.
- Throttle login and token endpoints; add IP allowlists for admin consoles; alert on impossible travel and brute-force patterns.
RBAC, tenancy, and data boundaries
- Design a role→permission matrix with stable IDs; store permissions in the database, not in code, to enable safe migrations.
- Combine RBAC with ABAC: tenant_id, project_id, data_classification; default-deny on resources; secure by query, not by UI.
- Prevent vertical escalation: forbids self-assignment to privileged roles; require break-glass approval with expiry.
- Emit immutable, structured audit logs; include actor, subject, scope, IP, and request_id; redact secrets and tokens.
- In your workflow automation app builder, scope node execution and webhooks to tenant and role; sign and timestamp workflow callbacks.
- In the AI web design tool, gate pages and components with server checks; never trust client-side toggles for access.
- Test policies as code (e.g., OPA); add unit tests for critical authorization decisions.
Payments and monetization
- Use a PCI-DSS Level 1 processor; tokenize cards; never store PAN, CVV, or raw webhooks.
- Validate signatures on webhooks, enforce idempotency keys, and reject stale replays with timestamps and nonces.
- Compute pricing server-side; enforce currency, tax, and tier limits; separate billing tenant from app tenant data.
- Require SCA/3DS where applicable; log refunds, disputes, and proration with actor context.
Model-specific safeguards
- Sanitize prompts; strip secrets; bound model tools; apply allowlists for external calls.
- Validate model outputs against schemas; block risky commands; moderate content and PII before storage.
Cloud deployment with Slashdev Cloud
- Isolate dev/stage/prod; run private networking with WAF; terminate TLS with modern ciphers.
- Pin dependencies, produce an SBOM, run SCA/SAST, and container image scanning in CI; sign and verify images.
- Codify everything (IaC); enable autoscaling limits, runtime policies, and workload identity; test disaster recovery regularly.
- Can a viewer read another tenant's invoice?
- Are admin endpoints behind SSO and IP allowlists?
- Do webhook verifications reject replays?
- Are tokens short-lived and rotated?
- Do logs redact secrets consistently?
- Are workflow webhooks signed and scoped?
- Is pricing computed only on the server?
- Does IaC recreate environments consistently?