Code Audit Framework: Exposing Performance, Security, and Scale Gaps
Executives ask for velocity; systems demand discipline. This framework shows how to audit C# .NET application development, Node.js backend development, and LLM orchestration and observability with the rigor of a production readiness review. Apply it quarterly, treat findings as backlog items, and tie each to measurable risk or revenue impact.
Establish an audit baseline
- Define SLOs: p95 latency, error rate, and cost per request/token. Without targets, every fix is subjective.
- Instrument first: OpenTelemetry traces, RED/USE metrics, and structured logs with request IDs across services.
- Capture a two-week trace sample under real traffic. Synthesize gaps via flamegraphs and dependency maps.
Performance hotspots to hunt
For C# .NET application development:
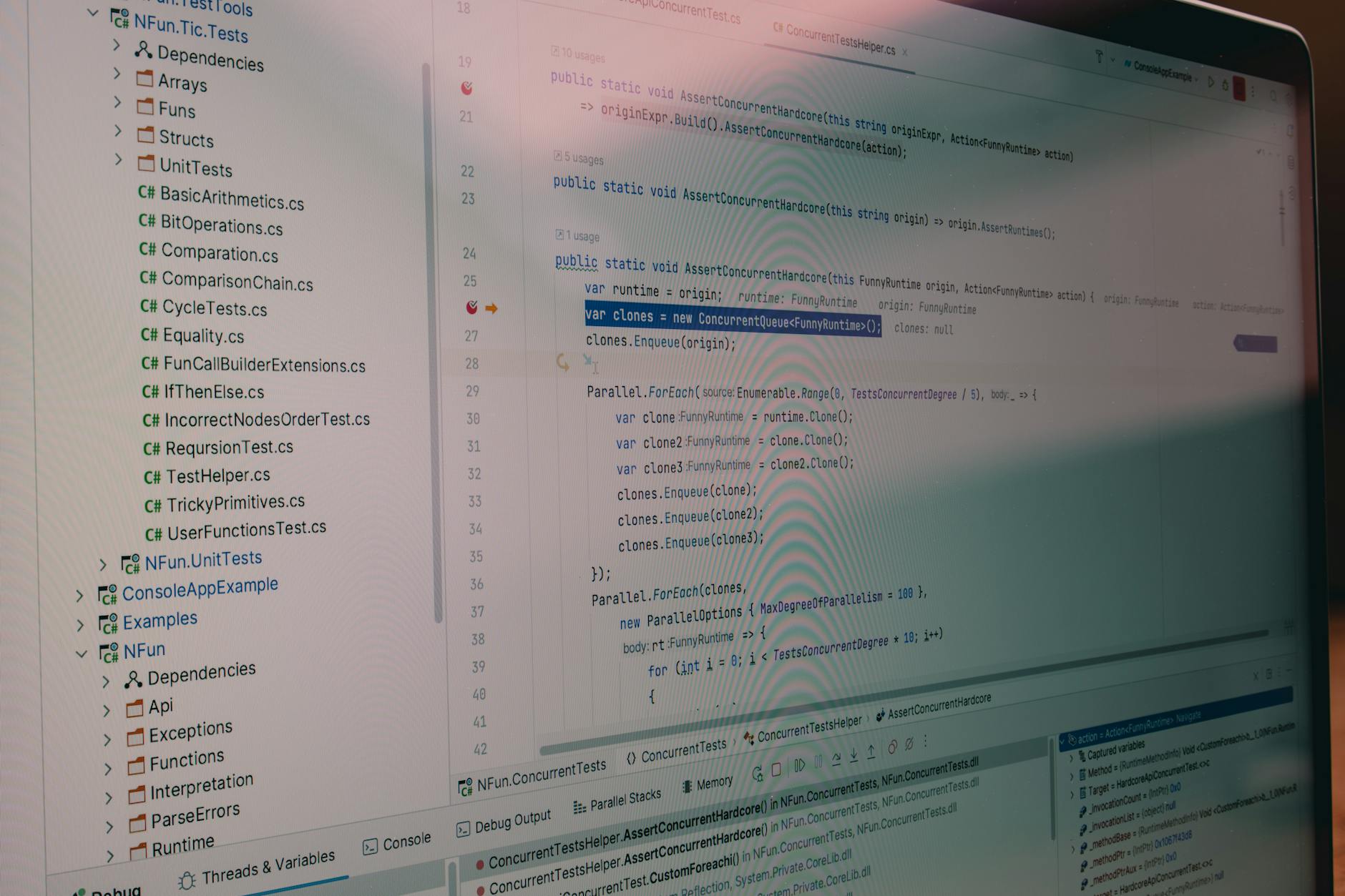
- Use BenchmarkDotNet for micro-benchmarks on hot code paths discovered from traces, not guesswork.
- Replace per-request HttpClient with HttpClientFactory; pool SocketsHttpHandler; verify DNS refresh settings.
- In EF Core, enable compiled queries for high-frequency reads; profile N+1 via Include/AsSplitQuery; watch async streams.
- Eliminate LOH pressure with pooled arrays and Span usage; confirm no accidental boxing in logging paths.
- Measure GC pauses with PerfView; tune Server GC vs Workstation; cap gen2 allocation storms.
For Node.js backend development:

- Run Clinic.js and autocannon; identify event-loop stalls over 50 ms; offload crypto/compression to worker threads.
- Ensure one database client per process with internal pooling; prevent per-request connections.
- Adopt Fastify for lower overhead; use pino async logging; batch logs to avoid fs sync churn.
- Cluster or PM2 only when CPU-bound; pin containers with CPU sets; prefer horizontal pods over overstuffed clusters.
System-wide gains:
- Cache with explicit TTLs and stampede protection; track cache hit rate by keyspace in metrics.
- Add idempotency keys on write endpoints; time-box downstream calls; apply exponential backoff with jitter.
- Run load tests that mirror traffic shape (burstiness, payload mix); validate p95 under 2x expected load.
Security surfaces you cannot ignore
- Threat model by data flow, not by repo. Document trust boundaries, auth contexts, and outbound calls.
- Supply chain: lockfiles reviewed on each release; generate SBOM; verify package signatures; block typosquats.
- .NET specifics: prohibit insecure deserialization; validate Regex with timeouts; use DataProtection APIs for secrets at rest.
- Node specifics: scan for prototype pollution, unsafe eval, unguarded JSON parsing; isolate dev tools from runtime builds.
- Secrets: no env leakage in logs; rotate keys automatically; enforce mTLS for east-west traffic; pin outbound TLS.
- AuthZ: move from role checks in controllers to policy-based authorization; add explicit deny logs with subject, action, resource.
- DAST against staging mirrors; fuzz critical parsers; capture WAF anomaly scores in traces.
Scalability and resilience patterns
- Backpressure at ingress: queue depth, drop policy, or 429 with Retry-After; never infinite buffers.
- Bulkheads: separate pools for read vs write traffic; isolate dependency clients per service.
- Circuit breakers with success thresholds; publish breaker state to metrics and Slack for visibility.
- Database scale: audit slow queries; add covering indexes; consider read replicas or CQRS for report paths; verify pool exhaustion alerts.
- Data growth: partition tables by time or tenant; schedule archival; benchmark compaction windows.
LLM orchestration and observability
- Gateway pattern: centralize providers, prompts, safety, and cost limits; persist request/response envelopes with versioned prompt templates.
- Token budgets: set max tokens per route; enforce retries with decrementing budgets and provider failover.
- Prompt hygiene: E2E tests with red-team prompts; assert refusal rates; scan outputs for PII using classifiers.
- Caching: semantic cache for deterministic prompts; eviction keyed by model, temperature, and template hash.
- Observability: include semantic spans for retrieve, rerank, generate; log token counts, latency, cost, and safety flags per span.
- Drift detection: weekly eval sets with golden answers; alert on BLEU/ROUGE/accuracy deltas beyond thresholds.
Remediation operating model
- Create an "Audit PR" label. Each finding requires a hypothesis, metric, owner, and rollback plan.
- Ship small: one change per deploy behind feature flags; compare baseline vs candidate with canary metrics.
- Quantify wins in dollars: latency cut x conversions; downtime avoided x SLA penalties; token savings x LLM bill.
- Partner smart: when bandwidth is thin, firms like slashdev.io provide vetted remote engineers who can execute changes quickly without sacrificing rigor.
Quick diagnostic checklist
- Do traces cover 95% of routes with database, cache, and external spans?
- Are p95 goals met during failure simulations (dependency 50% errors)?
- Is there a single source of truth for secrets and key rotation events?
- Can you replay a production incident locally from logs and spans within 15 minutes?
- Are LLM prompts, costs, and refusal rates visible per tenant and feature?
- Does every new endpoint document idempotency, rate limits, and SLOs?
The strongest audit culture treats code as a living asset. By making performance, security, and scalability testable-and by embedding LLM orchestration and observability into the same backbone-you replace anxiety with evidence. That is how teams turn ambitious roadmaps into dependable reality.




