Code Audits That Scale: Enterprise Speed, Security, and Savings
Enterprise code audits must expose measurable gaps in performance, security, and scalability; this framework emphasizes baselines, layered diagnostics, prioritized remediation, and CI guardrails that prevent regressions from creeping back into React and Next.js platforms.
Baseline Signals
Start with system-level truth, not anecdotes: p95 and p99 API latency, Apdex, error rates, Core Web Vitals by route, TTFB for SSR, hydration time, and DB query timings from connection acquisition through result materialization. Instrument Next.js with per-route server timings, edge versus origin splits, cache hit ratios, and RUM broken down by class; add React Profiler traces to detect wasted renders, component waterfalls, and effects during critical interactions. For databases, enable slow query logs, sample production traffic, capture execution plans, and profile connection pooling; map every endpoint to its read and write patterns, including bursts, tail latencies, fan-out, and cross-service transactional dependencies. Document baseline thresholds tied to revenue moments, like search results time to first product, checkout submit to confirmation, and dashboard initial render; your audit success criteria must be business aligned, not only technically elegant.
Performance Gaps
In Next.js, misuse of SSR where ISR or SSG suffices crushes concurrency; push non-personalized routes to ISR with revalidate windows, stream with suspense, and move heavy transforms to edge functions backed by regional caches. Apply bundle discipline: analyze with next-bundle-analyzer, kill moment.js for date-fns, lazy-load admin panels, extract vendor chunks, and prefer React Server Components to avoid hydration costs, while memoizing expensive pure components and normalizing prop shapes. Database design and optimization matters than micro-optimizing JSX; fix N+1 queries with prefetching, add covering indexes matching filter, join, and sort order, adopt partial indexes for predicates, and evaluate read replicas with read-your-write strategies. Prefer streaming and backpressure across services; avoid chatty APIs with pagination that forces repeated waterfalls, collapse round-trips with batched queries, and measure both server CPU burn and client battery impact to quantify improved efficiency.

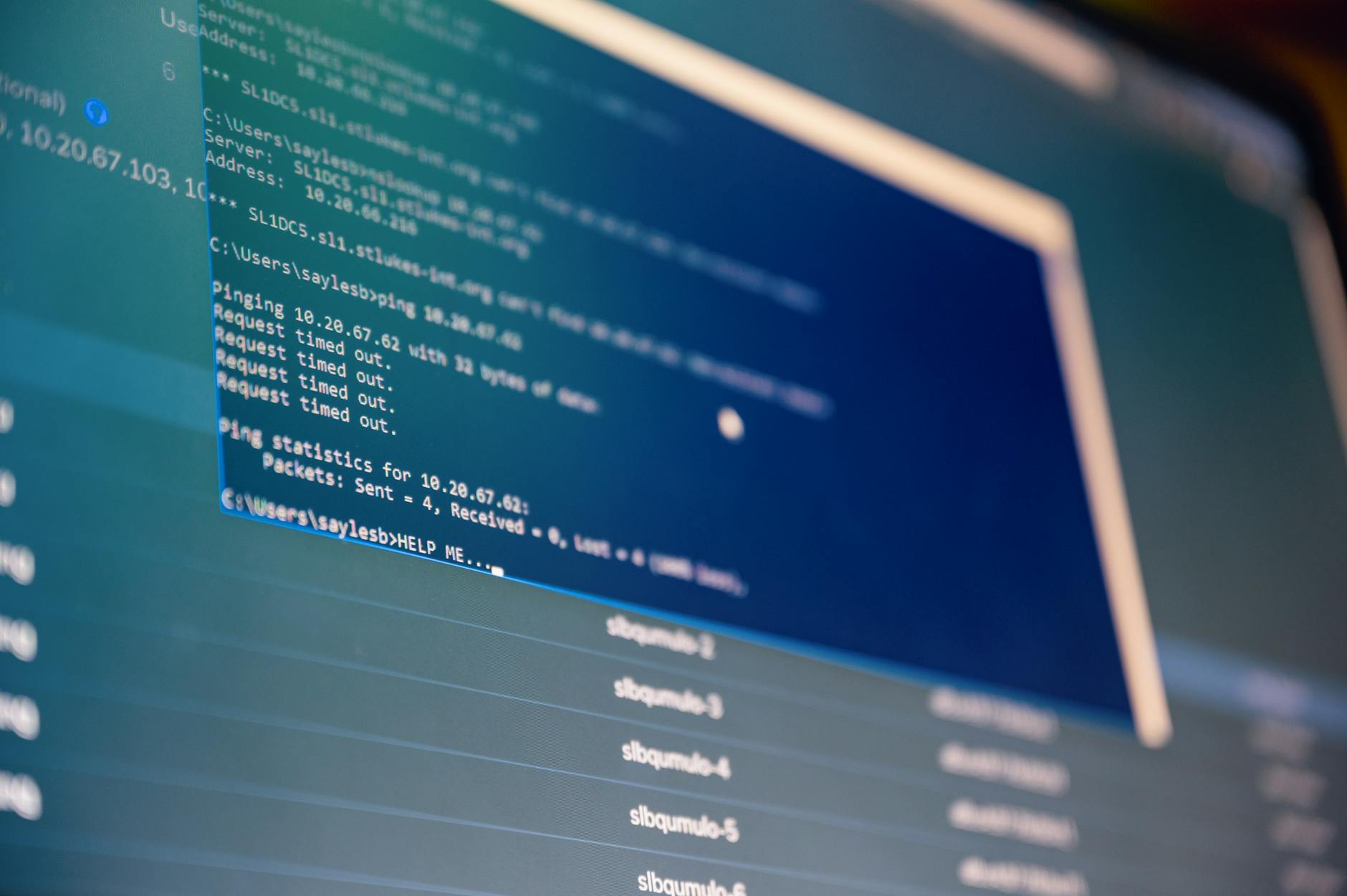
Security Gaps
Harden the platform with a default-deny posture: strict CSP with nonce or hashes, Samesite cookies, secure headers, SSRF protections on server actions, dependency allowlists, and secret scanning across repos, CI logs, and infrastructure state. Review React surfaces for XSS via dangerouslySetInnerHTML, untrusted markdown, or third-party widgets; enforce template escaping, sanitize inputs server-side, and ensure Next.js rewrites do not expose internal APIs or predictable build artifact paths to attackers. Run SAST and DAST with meaningful gates, ban vulnerable transitive versions, require signed commits, and audit infrastructure-as-code for least privilege, encrypted secrets, immutable images, dependable rollbacks, and workload identity over snowflake long-lived keys everywhere.
Scalability Gaps
Capacity issues begin in the data layer; verify cardinality, choose composite index order matching queries, partition by time or tenant, tune autovacuum and fillfactor, and cap runaway scans with statement timeouts and pagination strategies. Introduce read replicas with consistency expectations, queue write-heavy workflows, and collapse chatty updates into idempotent batches; verify connection pooling saturation and configure circuit breakers, backoffs, and retries that won't amplify thundering herds during incidents. For Next.js at scale, prefer edge rendering for geo-sensitive personalization, use ISR for catalog pages, stream server components, and precompute aggregates; monitor origin egress, CDN hit rates, TTLs, and stale-while-revalidate behavior under fault injection. If you are a Next.js development company or provide React development services, baseline concurrency by region, validate autoscaling thresholds, and chaos-test draining nodes, warming caches, and restarts to prevent request storms during major releases.

Workflow Guardrails
Codify the audit in pipelines: Lighthouse CI budgets for LCP and TTI, bundle budgets, k6 load tests for p95, SAST gates, DB migration checks, and snapshot query plans to detect Cartesian explosions before merging. Lock database performance with contract tests: given seed data shapes, the ORM call must hit a covering index and deliver bounded rows; fail the build if row estimates or join strategies drift beyond tolerances. Make wins permanent by publishing a runbook linking symptoms to fixes, like CPU spikes from JSON serialization or slow page loads from render waterfalls, so new teammates can remediate without re-discovering brittle tribal knowledge.
Thirty-Day Playbook
Week one, baseline and instrument; week two, prioritize cost-to-impact gaps; week three, ship remediations behind flags; week four, roll out with budgets, dashboards, and on-call drills that validate resilience under synthetic and live traffic. Define success in dollars: reduce abandoned carts by shaving checkout LCP, improve lead form conversions with faster hydration, and cut infrastructure spend by eliminating queries and over-fetching that bloats CPU, egress, and carbon footprints.
Need seasoned engineers fast? slashdev.io delivers remote talent and agency expertise for business owners, startups.



