Scaling AI-Generated Apps: Performance, Testing, and CI/CD
AI can sketch your backend before lunch, but scaling it past pilot takes rigor. Whether you ship through no-code development, an automated app builder, or wire in an authentication module generator, treat the result like any distributed system: measurable, testable, and repeatable.
Establish performance baselines
Start by profiling the "golden paths" the builder created: sign-in, search, write, report. Define a latency budget per hop and propagate it in headers so services can self-shed under load.
- Budget: P50 150 ms, P95 400 ms, P99 900 ms per request; set hard timeouts at 1.2x budget.
- Cache: materialize hot queries; use async writes plus idempotent retry tokens to keep UX snappy.
- DB: auto-generate index hints from query plans; block deploys if new plans exceed 20% cost.
- Vector search: pre-warm embeddings; shard by tenant to prevent noisy neighbors.
- Backpressure: implement token buckets per API key; spill to queue when concurrency exceeds CPU cores.
Load and resilience testing
Test like your biggest customer already signed. Use k6 or Artillery for traffic shapes, and inject faults to validate graceful degradation.

- Traffic: ramp 1k→20k RPS, mix 80/15/5 read/write/admin; include burst and soak phases.
- Chaos: kill 1 pod/minute; add 5% latency to the DB; verify circuit breakers open and close cleanly.
- SLOs: alert on 5-minute burn rate; autoscale on queue depth, not CPU.
- Data: replay masked production traces to catch schema or prompt edge cases.
CI/CD for generated code and pipelines
Regeneration is a feature-and a risk. Pin generator versions, require deterministic outputs, and codify expectations as tests.
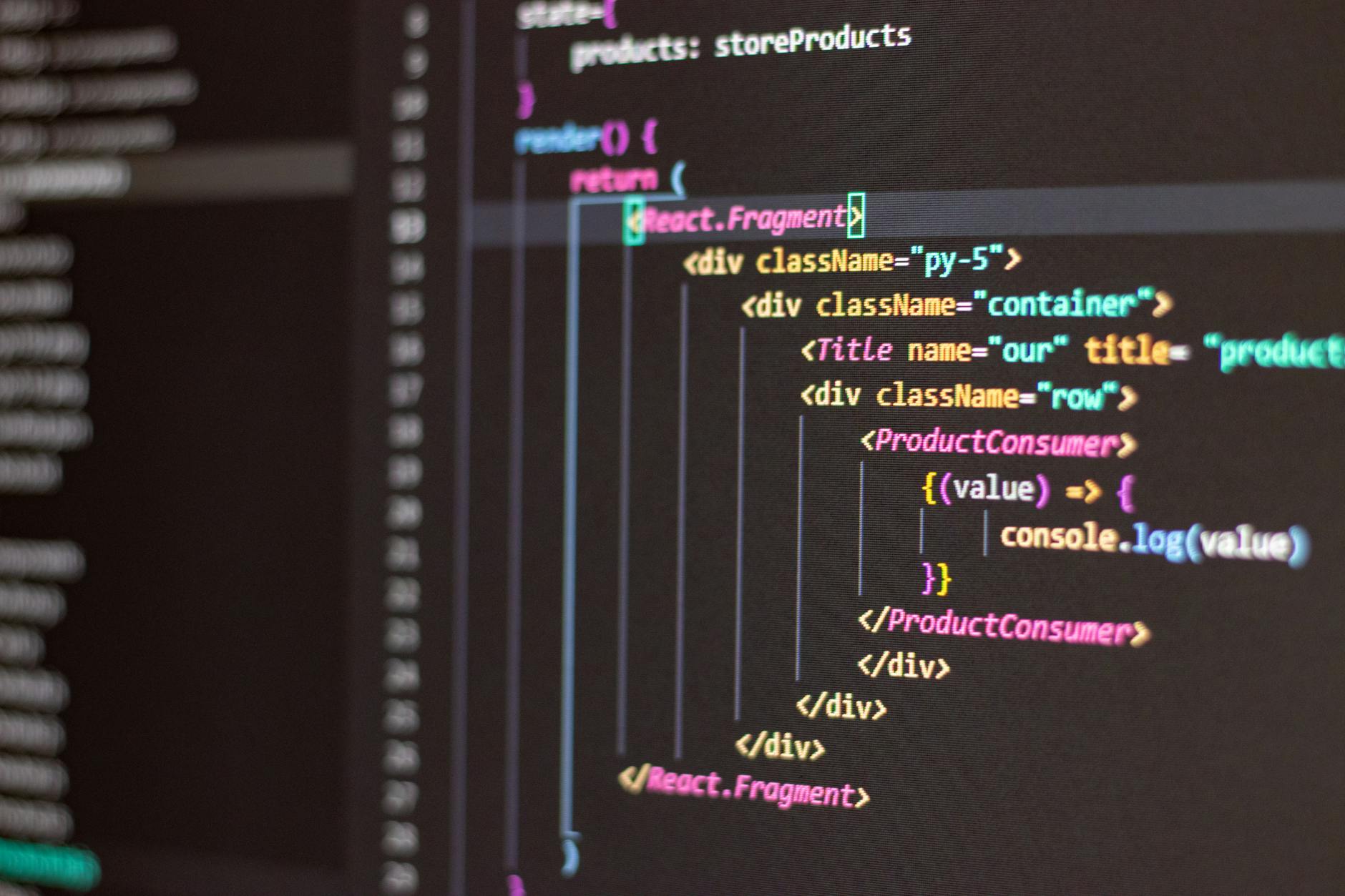
- Contracts: OpenAPI and JSON Schemas become the source of truth; run contract tests on every PR.
- Ephemeral envs: spin per-branch stacks with seeded tenants; destroy after checks complete.
- Migrations: run shadow writes and compare row counts/hashes before cutover; gate on zero drift.
- Security: SAST/DAST, SBOM, and dependency signing; attest builds with Sigstore.
Authentication at scale
Your authentication module generator should emit MFA, device binding, and risk scoring hooks by default. Tune for throughput without weakening posture.
- JWTs: keep under 2 KB; rotate keys with zero-downtime overlapping kid windows.
- Sessions: pin to region; fall back via sticky routing; cap refresh at 30 days.
- Abuse: per-IP and per-identity rate limits; proof-of-work on suspicious flows.
Observability that understands AI
Track prompt/version drift like code.
- Attach model, prompt hash, and dataset tag to every trace/span and analytics event.
- Compare baseline vs. current token usage and error taxonomy weekly; alert on 10% shifts.
Case snapshot
A B2B triage app built with an automated app builder scaled from 200 to 18k RPS by pinning generator versions and moving session issuance to edge workers. Result: P95 latency fell 38%, auth failures dropped 72%, and infra spend per ticket decreased 41%.
Executive checklist
- Define budgets, then wire them into code.
- Automate contracts, migrations, and security attestation.
- Test with real shapes, real faults, and masked data.
- Instrument prompts and models like dependencies.
- Ship small, reversible changes; flag, don't fork.



