Enterprise Security Checklist for AI-Generated Apps
AI-built software moves fast, but attackers move faster. Whether you ship with a no-code AI app builder, assemble an admin dashboard template AI, or plug in a billing and invoicing module AI, your security posture must be deliberate, testable, and automated. Use this checklist to harden authentication, RBAC, and payments without slowing product velocity.
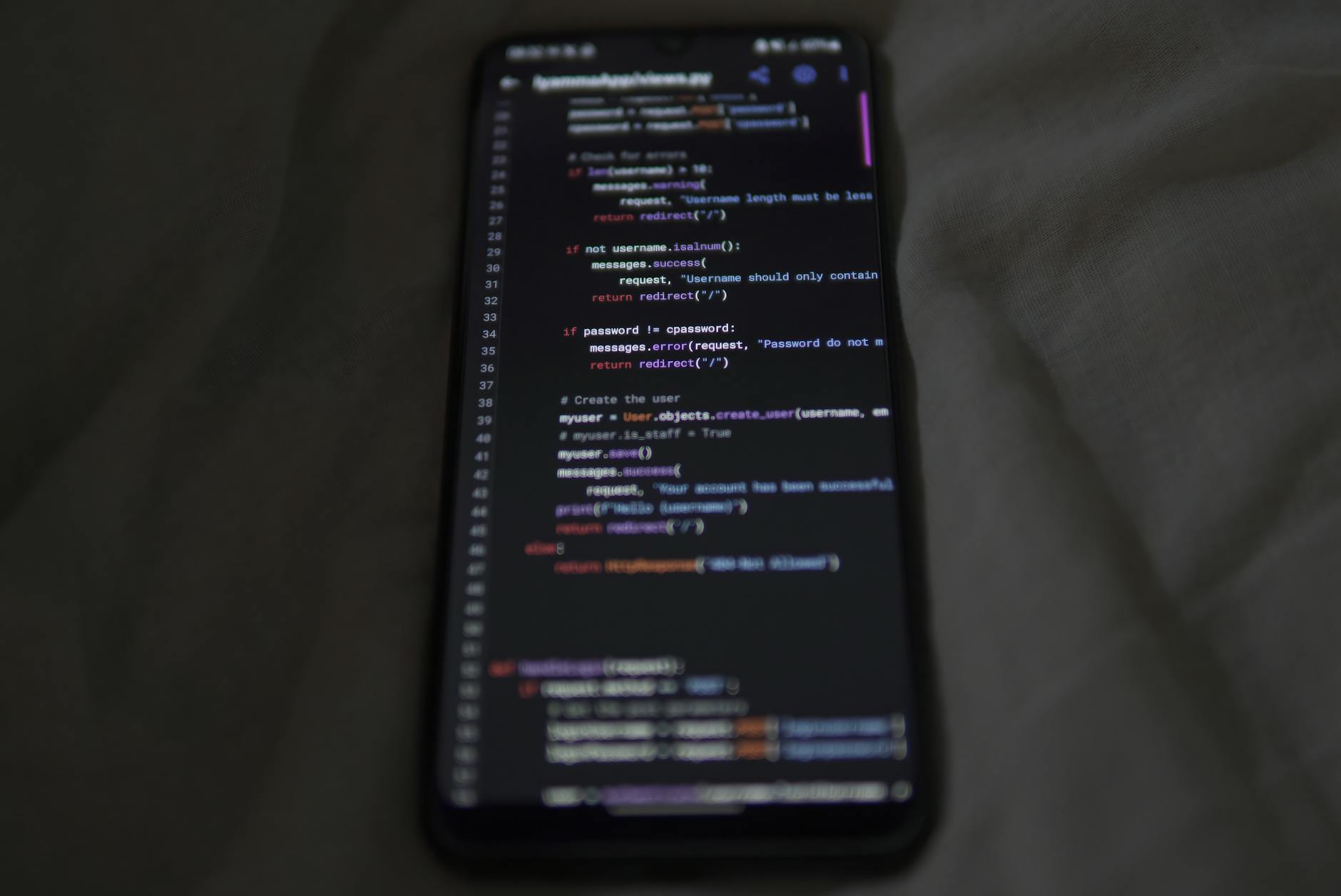
Identity and authentication
- Adopt OIDC with PKCE; forbid implicit flow; rotate client secrets and JWT signing keys on schedule.
- Enforce MFA for admins; require WebAuthn or TOTP; block SMS fallback for privileged roles.
- Use short-lived access tokens, refresh tokens with rotation, and sliding sessions; invalidate on password or factor change.
- Implement passwordless for customers; rate limit login and signup; add CAPTCHA only after risk-based triggers.
RBAC, tenants, and data boundaries
- Model roles and granular scopes; store policies as code; review diffs like any other PR.
- Use tenant IDs in every query; add row-level security; verify cross-tenant isolation with automated tests.
- Create service accounts per integration; grant least privilege; sign all internal API calls.
- Log every permission decision with actor, resource, scope, and result; ship logs to immutable storage.
Payments, billing, and invoicing
- Keep card data out of your app; use PCI-DSS compliant processors; tokenize everything.
- Verify webhook signatures and replay windows; require idempotency keys for all payment mutations.
- Validate currency, amount, and tax inputs server-side; lock historical tax rates; make invoices tamper-evident.
- Separate billing tenants from app tenants; restrict financial exports; reconcile payouts daily with alerts.
Admin dashboard hardening
- Guard dangerous actions with just-in-time reauthentication and step-up MFA; show signed diffs before apply.
- Enforce CSP, CSRF protection, and same-site cookies; disable inline scripts in the admin dashboard template AI.
- Use feature flags with blast-radius limits; require approvals for production toggles; auto-expire flags.
AI and data protections
- Scan prompts and uploads for PII; mask before storage; encrypt at rest and in transit with modern ciphers.
- Defend LLMs against prompt injection using allowlists, output schemas, and tool permission scopes.
- Never let model outputs change policy; validate with deterministic code paths and business rules.
Operations and assurance
- Pin dependencies, produce SBOMs, and sign artifacts; gate deploys with SLSA or similar checks.
- Stage canary releases; add WAF and RASP; run chaos and backup restores weekly; practice incident response.
- Codify the checklist as tests in CI; fail builds on missing controls; publish a living security README.
Field notes
A fintech built on a no-code AI app builder cut delivery time by half yet passed audits by enforcing OIDC, tenant isolation, and signed billing webhooks. Another team templatized an admin dashboard template AI with reauth on exports and could trace every role change. Treat this checklist as code, and your speed becomes an advantage-not a risk.