Security Checklist for AI-Generated Apps: Auth, RBAC, Payments
AI speeds delivery, but security debt compounds faster. Whether you ship with a no-code AI app builder, stitch microservices, or drop in an admin dashboard template AI, use this pragmatic checklist to ship safely at enterprise scale.
Identity and authentication
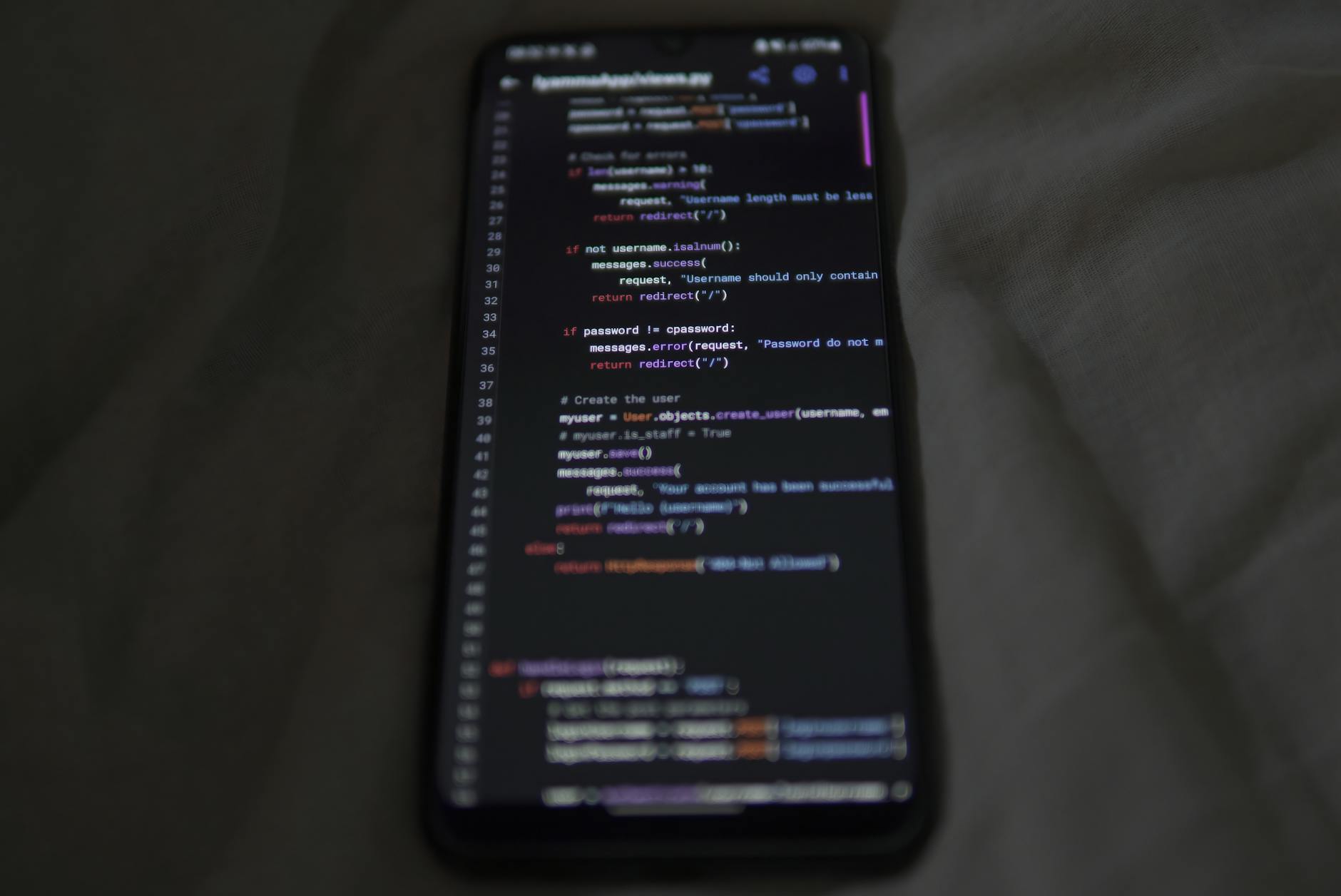
- Adopt OIDC with short-lived tokens; prefer PKCE for public clients and rotate signing keys quarterly.
- Mandate MFA; add WebAuthn for admins and finance roles to block SIM-swap attacks.
- Use secure session cookies (HttpOnly, SameSite=Strict) and device-binding for high-risk flows.
- Scope OAuth permissions narrowly; never let the model request escalated scopes on a user's behalf.
- Throttle and detect credential stuffing; instrument bot challenges on password, OTP, and magic-link endpoints.
Authorization and RBAC
- Define a role-permission matrix per resource; include negative tests (e.g., "viewer cannot export PII").
- Centralize policy as code (OPA/Casbin); evaluate server-side on every request, not just in UI.
- Add ABAC for enterprise: attributes like department, region, data sensitivity, and record owner.
- Run permission drift reports; snapshot nightly and alert on unexpected grants in the admin dashboard template AI.
- Log every admin action with who, what, when, where (IP/device), and justification comment.
Payments, billing, and invoicing
- Keep card data out of scope with tokenization; accept cards via hosted fields; stay aligned to PCI-DSS SAQ A.
- Validate webhook signatures and replay-protect with idempotency keys for checkout and refunds.
- In a billing and invoicing module AI, verify amounts server-side, cap discounts, and require dual approval on credits.
- Encrypt invoice PDFs; embed tamper-evident hashes; store a canonical copy in immutable storage.
- Handle tax/VAT rules by jurisdiction; test edge cases: free trials, proration, failed renewals, partial refunds.
Data security and AI-specific risks
- Classify data; tag PII/PHI at ingestion; enforce per-tenant encryption keys and TLS 1.2+ everywhere.
- Redact secrets from prompts and logs; constrain tools/functions so the model cannot hit privileged APIs.
- Pin model versions and dependencies; ship an SBOM; sign artifacts; verify supply chain at deploy time.
- Isolate embeddings/vector stores by tenant; apply row-level security and hard query limits.
Monitoring, testing, and response
- Emit structured audit logs; stream to a SIEM; alert on permission changes, payout edits, and role escalations.
- Red-team prompt injection against auth, RBAC, and payments; add canary prompts to detect jailbreaks.
- Practice restore drills; define RTO/RPO; maintain on-call runbooks and customer comms templates.
Deployment snapshot
- Secrets in vault, not env files; least-privilege cloud roles; private egress for third-party APIs.
- Preflight checks block deploy if compliance tests fail; approvals enforced for production migrations.
Apply this list whether you assemble with a no-code AI app builder, code by hand, or customize an admin dashboard template AI. Review quarterly, tie controls to owners, and measure outcomes. Automate evidence collection to satisfy audits without slowing releases down.